Getting control of service account sprawl
Almost all large organizations suffer from extreme service account sprawl, perpetuating the unmanaged, uncontrolled expansion of their privileged account attack surface. That’s why we published our eBook “Service Account Security For Dummies.” It was written to help our customers get control of their numerous service accounts and manage them more effectively.
So, how do you get there? Here are our service account best practices designed to help you manage and safeguard your service accounts from neglect, abuse, or exploitation.
5 service account best practices:
1. Discover your service accounts
How can you protect your service accounts if you don’t know where they are? All too often I hear from companies that the biggest barrier to protecting these accounts is fundamentally just not knowing where they are, or how many exist. IT teams are aware they may have these “backdoor accounts” that allow users and cybercriminals to bypass proper controls and auditing in order to compromise these accounts. They also know malicious insiders can create service accounts to gain access to sensitive information and go undetected for months or even years. But they feel powerless because they can’t discover and/or continuously identify service accounts. There are simply not enough resources to manage it properly with manual methods.
Delinea has a free tool to get you started in your discovery process. Delinea’s Service Account Discovery Tool measures the state of privileged access entitlements in Active Directory service accounts and exposes areas of highest concern. After running the Discovery Tool you receive a customized, prioritized risk report you can download and share.
Delinea has many free tools like the one mentioned above—you'll find them here: Our top 15 PAM Tools.
2. Document, classify, and inventory your service accounts
Very few organizations have the time, tools, or inclination to inventory their service accounts. As a result, many service accounts may exist without any oversight or accountability. In light of recent events involving the compromise of these accounts, IT teams need to create a record that explains why accounts exist, which humans have credentials to access them, and which service(s) depend on each service account. And don’t forget to include when the service account should be reviewed, deactivated, or deleted.
Look for advanced solutions that can automate the process of finding unmanaged and unknown accounts. This can greatly alleviate the amount of time and resources required to document, classify and inventory service accounts.
3. Secure access to each service account
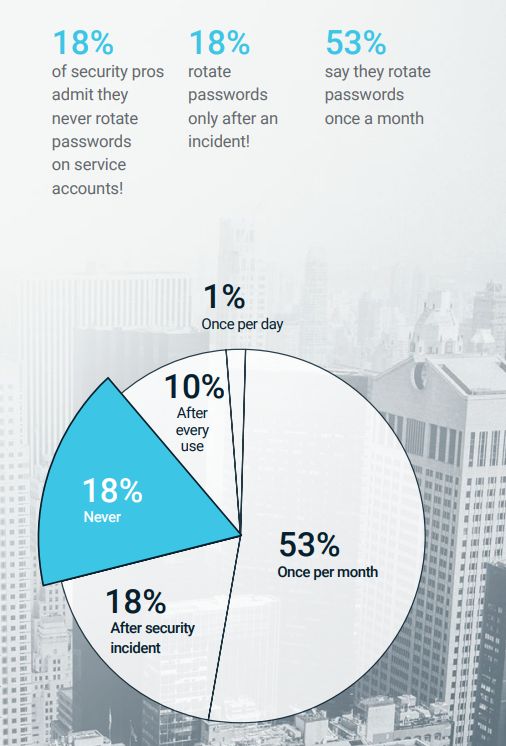
As with any privileged account, customized credentials must be associated with each service account. You should already have them in a centralized vault, and credentials should be limited only to necessary access. When you first discover a service account, for example, change passwords immediately and put it on a rotation schedule along with a way to monitor and ensure someone else hasn’t gained access or changed credentials outside the system. You’ve got to use an automated privilege access management (PAM) solution to accomplish this effectively and efficiently.
Keep in mind that not all service accounts use passwords; some are set to the system and some use SSL Keys, which are a commonly used means of authentication within enterprise IT environments. Because of a lack of visibility, IT groups often overlook these credentials when building a privileged access security strategy.
4. Establish governance and assign accountability
Over the long term, you must implement a governance plan for managing your service accounts. Your plan has to assign ownership to individual users and build a role-based permission system that encompasses administrators, requesters, owners, and approvers.
Companies should standardize when service accounts are created in accordance with their company’s security policies. When setting up an account, it is critical to determine which organizational or business unit the service account should be assigned to and any other AD attributes required.
Establish a workflow for requesting service account creation and the proper approval steps, along with a process for assigning account ownership. An individual IT manager, a business owner, IT admin, or a security staffer should be clearly designated as responsible for approving new account creation.
There is an excellent report from analyst firm KuppingerCole called “Privileged Access Governance” that will help you understand how to govern non-human service accounts and prevent insecure service account sprawl. It explains in depth how a new generation of automated Privileged Access Governance solutions can help you achieve and maintain service account control and security.
5. Automate service account governance (and keep your sanity)
When seeking to automate service account security from provisioning through decommissioning, answer several questions upfront. Your responses will confirm the requirements you need and want from any automated solution. For example:
- Who in your organization should be involved in the creation, approval, and ongoing management of service accounts?
- How often should the service account be reviewed? We recommend setting this according to internal policies and/or compliance requirements.
- If the account is renewable, can the account owner do it themselves or should the renewal go through the same approval process as when it was first created?
- In Active Directory, there are options for decommissioning an account. Do you want it to be disabled, expired, or deleted?
- What are the appropriate steps when you want to decommission a service account? Do you want the service account owner to do it or can a policy-guided tool do it automatically?