PAM for Incident Response
See how PAM helps you determine the extent
of a cyber incident and contain the damage.
Challenge
Firewalls and antivirus tools aren’t sufficient to detect and shut down sophisticated cyber attacks.
Risk
When privileged accounts are compromised, a breach can escalate into a cyber catastrophe.
Solution
To reduce incident response effort and cost, layer privileged access security across workstations and servers.
Do you know the signs of a privileged account attack?
The average time to detect and contain a data breach is almost 300 days. To reduce dwell time, you must know the early warning signs of a privileged account attack:
- Excessive failed login attempts
- Unusual password activity
- Activity demanding sudden increase in bandwidth
- Excessive activity outside of business hours
- Multiple logins with the same privileged account over a short period
- Privileged accounts accessed from unexpected IP address or countries
- Event logs with suspicious activity and event ID’s
- Legitimate user behavior inconsistent with the user's behavioral profile

Incident Response Plan
The incident response plan template contains a checklist of roles and responsibilities and details for actionable steps to measure the extent of a cybersecurity incident and contain it before it damages critical systems.
Validate identities and privileged account activity
When privileged accounts haven’t been used in some time or they’re used for the first time it’s important to validate if the activity is expected or suspicious. If it’s suspicious, you can trigger multi-factor authentication or peer review to ensure privileges are being used appropriately.
It is critical to enforce MFA policies consistently across all your regulated and business-critical systems to keep your organization secure and mitigate the risk of intrusion.
See how Server PAM validates identities and forces MFA at depth »

Dynamically rotate passwords for privileged accounts
Rotating passwords regularly and on-demand can help identify potential privileged account abuse by luring attackers into revealing themselves. Rotate passwords whenever possible for non-human privileged accounts and shared privileged accounts, especially after they have been used or disclosed.
Automation of password rotation creates a proven, repeatable process that can be applied consistently so security requirements aren’t forgotten. Advanced PAM software solutions are constantly on guard. They continuously check for issues and troubleshoot them right away.
See how Secret Server on the Delinea Platform manages passwords »

Continuously discover new and modified privileged accounts
Employees constantly download and deploy new applications and install new systems. Some may be known to IT, some may be “shadow IT,” installed without IT involvement.
When you don’t know where privileged accounts exist, you leave potential back doors for cyber criminals to bypass security controls. External threat actors may create accounts for later access and go undetected for months.
Automatic Discovery makes it easy to find privileged accounts so you can set policies to manage appropriately.
Discover rogue privileged accounts with the free PAM Discovery Tool »
Monitor and record privileged account activity
Session management provides detailed audit logs and searchable visual records of all privileged account activity for oversight and forensics after an incident.
Session management, monitoring, and control increase oversight and accountability so you can mitigate risks of account misuse. Even organizations with mature PAM programs don’t merely trust people are always doing the appropriate things with privileged access. Session management is used as a second pair of eyes to ensure best-practice PAM policies are followed.
See how Secret Server on the Delinea Platform manages passwords »

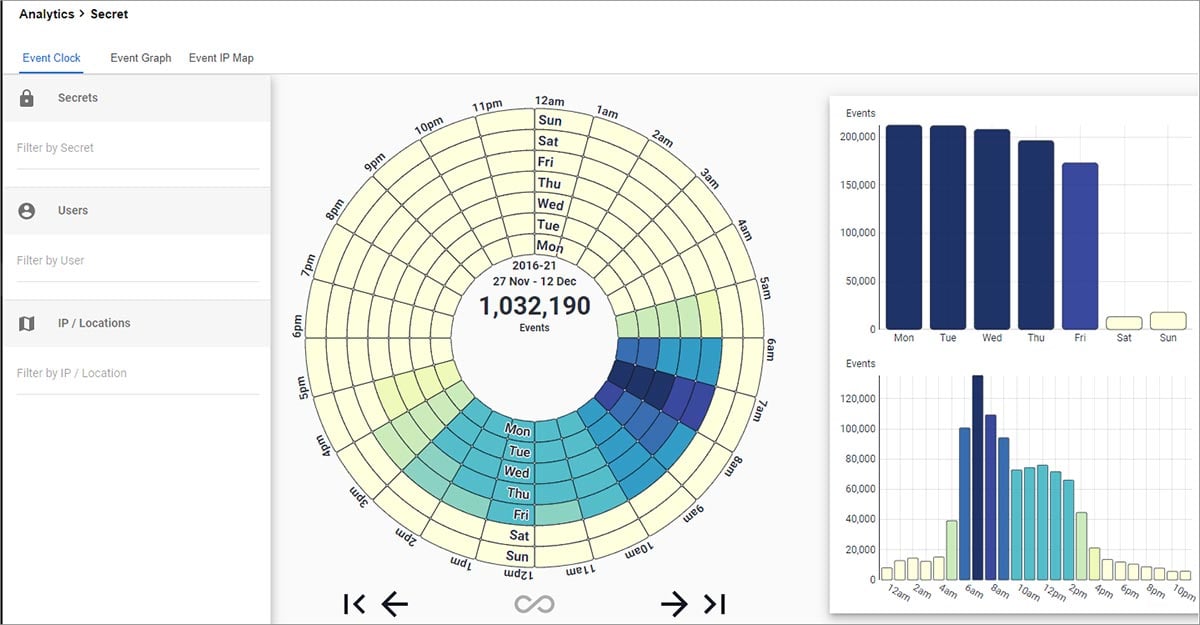
Automatically detect anomalous behavior
Behavioral analytics within advanced privilege management systems automatically detect privilege account activity that is out of the ordinary. Alerts of suspicious behavior regarding privileged accounts can be sent to incident response teams for further investigation and action.
Advanced machine learning analyzes privileged account activity so you can spot problems and measure the extent of a breach. Your PAM solution software can send alert notifications in Slack or open a ticket in ServiceNow when risks pass certain thresholds.
See how Privileged Behavior Analytics detects behavior and alerts teams for response »
PAM Solutions for Incident Response
Full-featured, free software trials get you up and running fast
Secret Server
Discover privileged accounts, vault credentials, ensure password complexity, delegate access, and manage sessions.