Enforce Principles of Least Privilege on Servers
Protect privileged access to servers with identity consolidation and centralized management of just-in-time and just enough privileges across Windows, Linux, and Unix servers.
Protect servers with seamless policy-based authorization controls and MFA at-depth
Enhance security
& mitigate risk
& mitigate risk
Centrally administer just-in-time and just-enough privileges and provide identity assurance with multi-factor authentication enforcement at system login and at privilege elevation to prevent lateral movement.
Consolidate identities
& improve productivity
& improve productivity
Eliminate the large number of unmanaged local accounts and use enterprise directory accounts to access Windows, Linux, or Unix on-premise or in the cloud to limit identity sprawl and simplify workflows.
More easily audit
privileged activities
privileged activities
Leverage granular, host-based auditing and session recordings to identify potentially harmful privileged activities and demonstrate controls for compliance with unaltered audit data.
Enforce zero trust and least privilege best practices on Windows, Linux, and Unix servers in hybrid cloud environments
Delinea seamlessly and granularly controls privileged access to servers with just-in-time and just enough privilege elevation and provides identity assurance with layered MFA enforcement, to prevent lateral movement while increasing accountability.
Flexible delivery ensures regardless of your environment, you can protect and monitor server access
Privilege Control for Servers
Delivered on the cloud-native Delinea Platform, build on your enterprise vault by extending Privileged Access Management and layering security directly on your servers using enterprise identities.
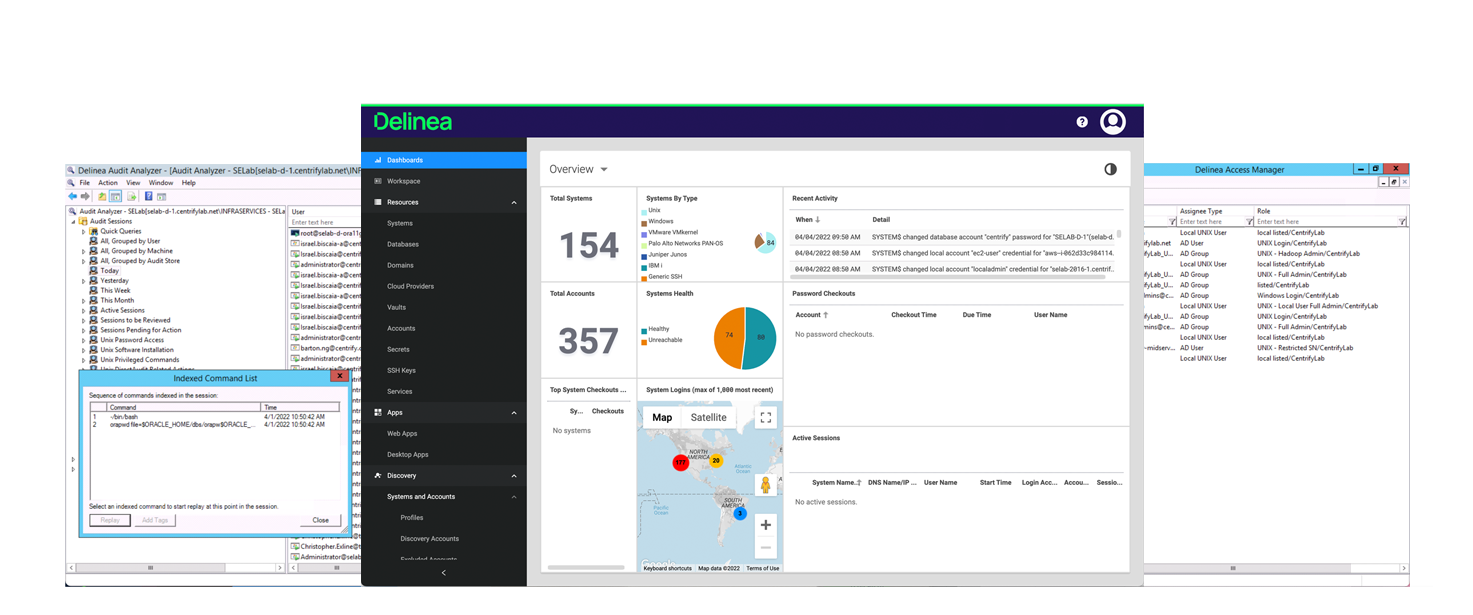
Privilege Control for Servers enables a clear line of sight across all privileged activity and access to servers with continuous discovery, adaptive authentication, host-based insights, policy management, and AD bridging.
Seamlessly manage just-in-time and just enough privileged access across Windows, Linux, and Unix servers while enforcing Multi-Factor Authentication (MFA) at log-in and privilege elevation for additional identity assurance.
Cloud Suite
With a standalone SaaS solution, consolidate identities and leverage multiple directory services such as AD, OpenLDAP, Ping Identity, and Azure AD, so modern enterprises can streamline privileged access to their servers.
Cloud Suite enables cloud transformation at scale. It empowers organizations to globally govern privileged access through centrally managed policies dynamically enforced on the server.
With Cloud Suite, organizations minimize their attack surface by establishing trusted machine identities and leveraging corporate identities for authentication, implementing just-in-time privilege, MFA enforcement, and securing remote access while auditing everything.
Server Suite
With a standalone on-premise solution, enforce least privilege best practices for servers and centrally manage policies from Active Directory
Server Suite unifies policy management for Windows, Linux, and UNIX within Active Directory. It empowers organizations to globally govern privileged access through centrally managed policies consistently enforced on the server.
With Server Suite, organizations minimize their attack surface by establishing trusted Active Directory machine identities and leveraging corporate identities for authentication, implementing just-in-time and just-enough privileges, MFA enforcement, and securing remote access while auditing everything.
Consistently enforce least privilege
Centrally manage privileged access and MFA enforcement policies in Active Directory (AD) (patented zones) or from most cloud identity providers. Single enterprise identity for user login.
Minimize risk with best practices
Align with regulations and best practices such as zero trust and least privilege to protect against threats like ransomware and data breach attacks.
Granular privilege elevation
Apply policies at the host level for fine-grained control of privilege elevation. Implement self-service workflows for automating just-in-time access requests.
Enforce adaptive MFA
MFA policies enforced at login and privilege elevation across Windows, Linux, and Unix for stronger identity assurance and cyber insurance demands.
More easily meet compliance requirements
Forensic-level audit trails and session recordings for security review, incident response, compliance, and full accountability.
Modern, scalable architecture simplifies the management of privileged access to complex server environments
Features |
|
Consistent privilege elevation policies across various identity providers |
|
Choice of cloud identity providers or Active Directory through patented Zone technology |
|
Multi-directory brokering |
|
Multi-Factor Authentication (MFA) enforcement at depth |
|
Granular host-based auditing and session recording |
|
Identity consolidation to reduce attack surface |
|
Consistent enforcement of zero trust and least privilege best practices |
|
Download the Server PAM datasheet for more information.
Request a Trial
Industry-leading identity consolidation and just-enough and just-in-time access for servers
Simplify user authentication and passwordless login to servers by consolidating identities across Active Directory and the most popular cloud directory services while enforcing MFA for stronger identity assurance.
Enforce the principle of least privilege across IT infrastructure on-premise, and in the cloud.
Identify abuse of privilege, thwart attacks, and easily prove regulatory compliance with a detailed audit trail and session recordings that capture all privileged activity.

Enforcing least privilege on servers is a key part of extended PAM
The standard definition of PAM isn’t sufficient for the growing risk of cyberattacks. We believe PAM must address the exploding number of identities and today’s IT complexities.
Our products provide effective authorization controls for an identity-centric approach to security.
Multi-Directory Brokering
Multi-Directory brokering is designed to simplify administrative login to servers spread across the data center and IaaS platforms.
Adaptive MFA for Privileged Access
Delinea’s risk-based multi-factor authentication (MFA) for privileged access provides an extra layer of security that stops in-progress attacks on critical resources.
How to Apply Zero Standing Privilege
Secure access to modern hybrid cloud infrastructures that include Windows, Linux, and UNIX servers running on traditional bare-metal hardware, virtual systems, containers, and microservices.
Conversational Server Access Security
Your most critical data resides on local and cloud servers. Read this book for guidance on better protecting access to your servers.