Step 4: Access exploitation
There are many potential attack paths. I will stick to the two most popular: bugs in Windows OS/apps and humans.
Bugs in Windows Operating Systems and Applications
This is probably one of the oldest attack methods. It’s been around since the retro days of computing. Yep, around when I was still using an Atari ST 800 XL computer and writing programs in Atari BASIC.
Software has bugs. Ethical hackers participating in bug bounty programs get rewarded for discovering them and some companies make a business out of selling them. There are kernel bugs in operating systems and application bugs that allow attackers to use the software in an unintended way to gain initial access.
With the digital transition to virtualization, cloud computing, and DevOps, we’ve seen an increase in misconfigurations – typically from security not enabled by default – that leaves access open for everyone. The same security methods you use for traditional, on-premise tools are no longer sufficient.
Microsoft has improved Windows operating systems significantly over my near 30 years of using Windows – yes, even DOS days. I know; I am that old!
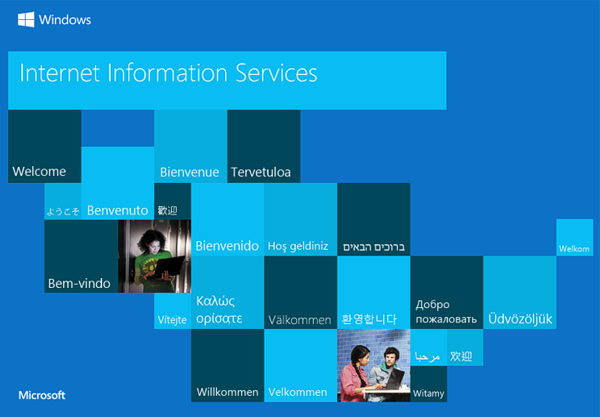
Windows is the best it’s ever been. Significant improvements in security, the patching process, and less frequent kernel exploits have made Windows more difficult to exploit. Once you introduce users and applications, however, security weakens. (But honestly what is the operating system without users and applications? It’s like a car without wheels or a driver).
The biggest security risk to Windows endpoints is using legacy versions. If you’re using Windows 7/8 or even XP – or, God forbid, you still have any Windows NT or Vista around – your security is like paper waiting for a windy day.
I’m originally from Belfast, Northern Ireland, where every day is windy.
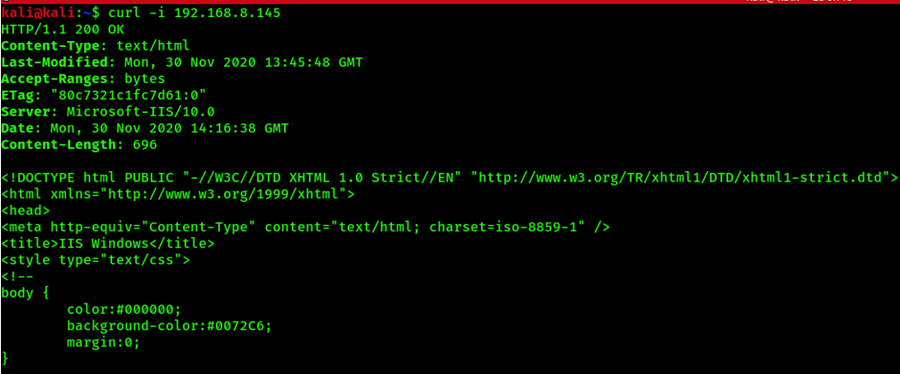
Just like operating systems, applications come in different flavors and security risks. Many application owners tend to install the default with everything checked, which is likely to introduce many features and bugs.
Almost all exploits against operating systems and applications involve at least one of the following:
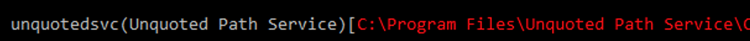
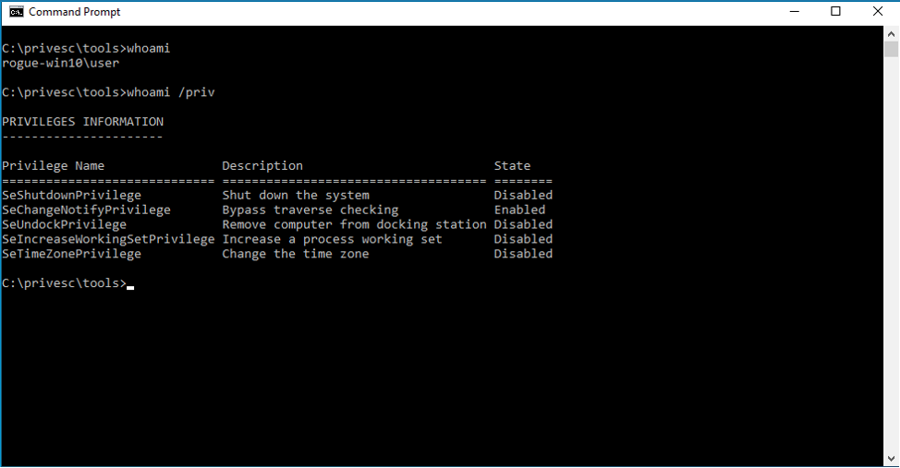
- Legacy OS with existing known exploits
- Unpatched system with existing known exploits
- Weak credentials – OS and applications
- Default credentials – OS and applications
- Misconfigured system
- Unpatched application with existing known exploits
- Misconfigured application
- Security not enabled
For web applications, I use the OWASP Top Ten:
1. Injection
2. Broken Authentication
3. Sensitive Data Exposure
4. XML External Entities
5. Broken Access Control
6. Security Misconfigurations
7. Cross-Site Scripting (XSS)
8. Insecure Deserialization
9. Using Components with Known Vulnerabilities
10. Insufficient Logging and Monitoring
Also, check out the 2020 CWE Top 25 Most Dangerous Software Weaknesses from MITRE.
Humans
Users are on the front line. They’re under attack from countless cyber criminals. Simply telling users to “click on less of the bad stuff” means we’re leaving them to tackle cyber threats alone. We must work together to make humans a strong link in cybersecurity defense.
Cyber criminals attempt to abuse trust by offering legitimate-looking services. One click on a hyperlink could install malware or ransomware. One shared password could provide personal information and credentials.
BTW, did you click on that hyperlink above?
I’m one of the good guys. As an ethical hacker, the links I set up will only take you to educational or maybe useless information.
But I do hope you at least hovered over the link to see where I was taking you.
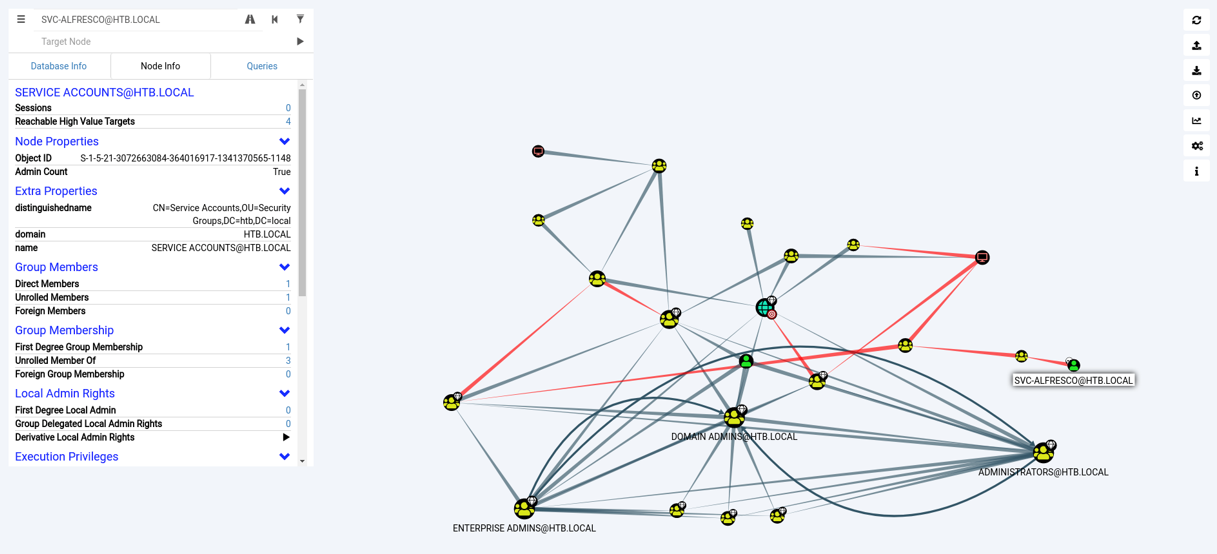
If I’m unable to gain access via an operating system or application, I turn to the users.
There are many ways to do this:
- Politely ask users for the password – some will actually hand it over
- Ask support to reset a user’s account for you (Twitter might remember this one)
- Phishing over the phone
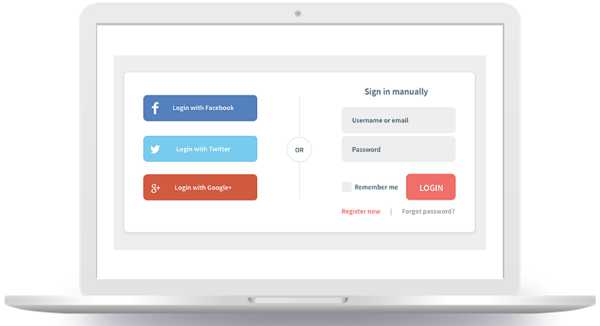
- Phishing, pretending to be a legitimate internet service
- Getting users to install a software update—aka a RAT (Remote Access Tool)
- Unattended laptops, especially if they’re logged in
- Man/Woman-in-the-Middle attack
- Using unsecured Wi-Fi or network
- Reused or weak passwords
One of my most successful phishing campaigns was enticing people to pay for speeding tickets. This had a high success rate because it triggered fear. People wanted to avoid spending money and save time.
Similar examples encourage people to click or log in to see:
- Parking fines
- Health insurance
- Health information
- IT surveys
- Unsubscribe buttons
Simply showing people a logon screen makes them want to enter their credentials.