To secure Windows endpoints against cyberattacks, it helps to think like a cyber criminal.
Cybercriminals look for the cheapest, fastest, stealthiest way to achieve their goals. Windows endpoints provide many opportunities to gain entry to IT environments and access sensitive information.
As part of the ethical hacking community, my ultimate goal is to help you secure your organization. That’s why I’m revealing the techniques and tools I employ during my hacking process.
There are six steps to an ethical hack of Windows endpoints:
- Step 0: Pre-Engagement
- Step 1: Passive Recon
- Step 2: Active Recon
- Step 3: Service Enumeration
- Step 4: Access Exploitation
- Step 5: Privilege Escalation
In this blog, I’ll cover steps 0-2 in depth. Those steps will take you through the preparation and research process.
The second blog in this series, Hardening Windows Endpoints Against Cyberattack: Part II, will cover steps 3-5. That’s when you’ll be able to bring together everything you learned.
Armed with this knowledge, you’ll be able to try your hand at an ethical hack to test your own organization’s defenses. You’ll also learn endpoint security strategies that empower you to block malicious hackers at every stage.
Step 0: Pre-engagement
The first step in an ethical hack is to determine the goals, target, and scope of activities. You should always ensure you do no harm. Make sure your plan adheres to an ethical code and stays within legal boundaries.
Confirm you have permission from the organization to run any hacking tools you’ll use. Are you permitted to target employees, or only systems and applications? This typically depends on how closely you want to simulate a real-world attack.
Test your toolset before you begin the active hack
If your organization has a lab environment, test your toolset there first, before you begin the active hack. If your actions will trigger alarms, you’ll know security controls are doing their job. If not, there may be misconfigurations.
Step 1: Passive recon
This next step is the same for practically all engagements. It helps me create what I call my attack path.
It’s amazing how much passive reconnaissance you can do with publicly available information.
Open-Source Intelligence (OSINT) is critical to any risk assessment of a company’s security, especially the hardening of systems and devices. With OSINT, a hacker can obtain publicly available information to gain access. The more information you gather, the better prepared you’ll be. At times I have found that when one attack path doesn’t work, a solid OSINT step allows me to quickly adapt.
During OSINT, passive recon involves two areas:
- Physical recon, such as hanging out near the target’s office location or glancing through windows, trying to gather information on security controls, guards, badge readers, fences, and any other physical security controls. You might try to identify employee information such as names, titles, badge types, phone models, laptop models, and maybe even try to snap a high-def photo.
- Online recon, using research and social engineering. You can create a blueprint of an organizational structure from social media. Job postings that include required skills can reveal tools the company is using, like operating system versions, applications, and even security solutions. You can also gather logos, email formats, corporate templates, email footers/signatures, and telephone numbers, through publicly available information.
Common tools for passive recon
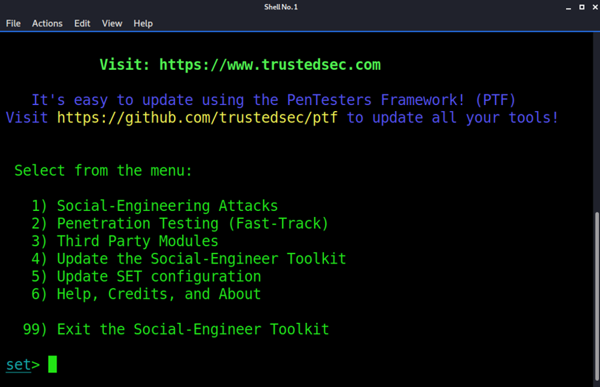
A few awesome OSINT and social engineering resources include:
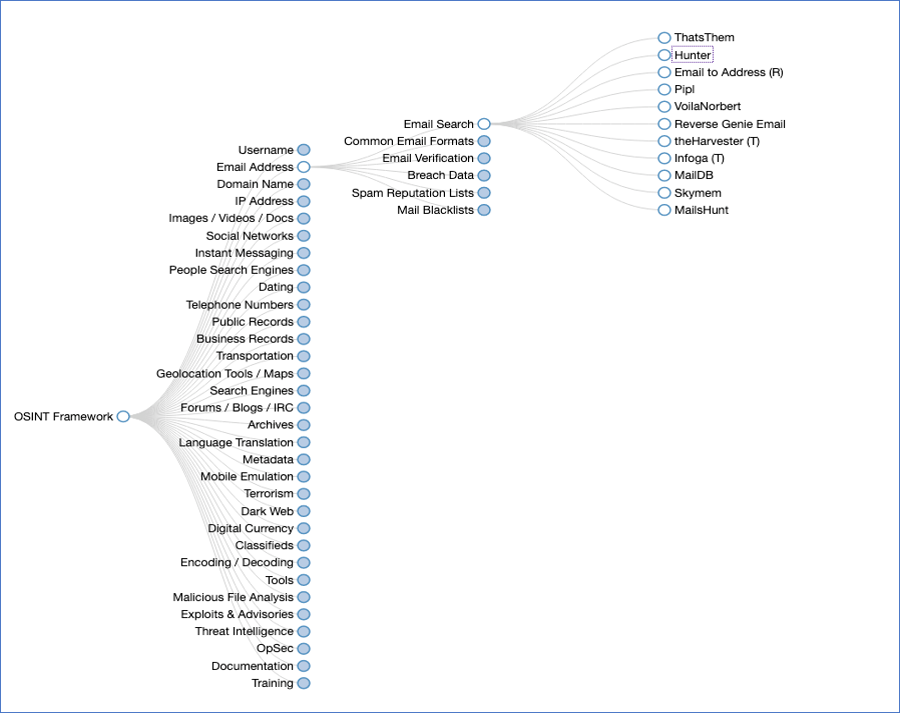
OSINT framework, focused on gathering information from free tools or resources.
Before moving on, always double-check hostnames, domain names, IP addresses, and everything else you’ve gathered during scoping or OSINT. The last thing you want is an ethical hack against the wrong company! One of my favorite stories about this is “The Courthouse.” Check it out on one of my favorite podcasts, DARKNET DIARIES.
How to protect against OSINT
Look at your organization through the lens of Open-Source Intelligence to block or divert attackers.
- Limit public information. Ensure your talent team doesn’t disclose information, such as security software you use, on a public website. If they must, they should be as vague as possible and only disclose vendors or version details during an in-person interview.
- Set traps. Leave breadcrumbs, such as intentionally disclosed email addresses. Using honeypots or deception technologies can alert you to OSINT attempts. I call this “Takeshi’s Castle Approach.” When you deploy Takeshi’s Castle, you’re giving attackers skipping stones and a fake door challenge, which will deter many. (I only wish this was a real cyber solution).
- Work with external open testers. Perform social engineering and OSINT gathering.
Train employees. Employees are on the front line of protecting your organization. Teach them to protect themselves at work and in their personal lives. For example, it’s common for employees to take a selfie to have lunch or meet with the team. Make sure they know to check what’s in the background, such as passwords on whiteboards, sensitive info, Zoom meeting IDs, and badge info.
- Empower employees. Employees shouldn’t be afraid to report incidents or ask for advice. The more they communicate, the earlier you can identify potential attacks.
Step 2: Active recon for Windows
I call this stage “knocking on doors and windows.” Those doors and windows can be public-facing servers, applications, web servers, Windows endpoints, and employees. I look for vulnerabilities and misconfigurations to gain an initial foothold.
Scanning and port enumeration
One of the most popular scanning and port enumeration tools is nmap, aka Network Mapper. It’s been around since 1997 when Gordon “Fyodor” Lyon made it available in Phrack magazine. This free, open-source utility is used for scanning, network discovery, and security auditing. It’s my go-to tool for getting visibility of the network. One book that stays near my desk is my nmap guide, which helps me figure out how to get the right scan and stay stealthy.
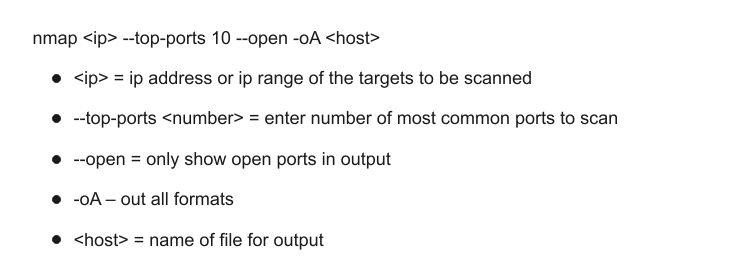
Nmap is extremely powerful. It can be complex so I will try to keep it a little simple. Below are a few examples of default scanning and port enumeration options I use. I tend to start quick and easy then move to slow and detailed. For now, I’ll go straight to the flag.
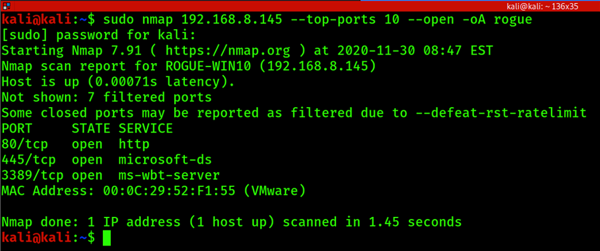
The Quick Port Scan
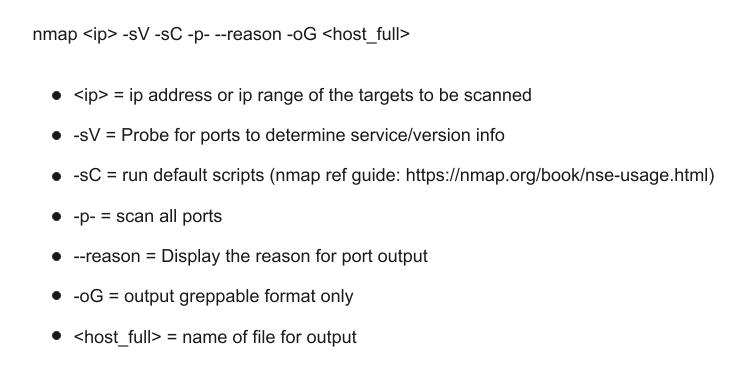
The Full Port Scan
This may take some time to run. Don’t forget UDP ports as well.
Other common options:
- -T4 = timing template to use T<0-5> (higher is faster)
- -A = enable OS detection, version, script scanning and traceroute
- -O = OS detection
- -sU = UDP Scan
- -sS = TCP SYN Scan
Additional common information gathering, scanning, and enumeration tools include:
- Netdiscover – Active/passive arp recon tool
- Zenmap – GUI for nmap
- Netcat – Networking utility
- Masscan – The fastest internet port scanner
- Legion – Automated recon and scanner with hundreds of integrations
- Dmitry – aka Deepmagic Information Gathering Tool
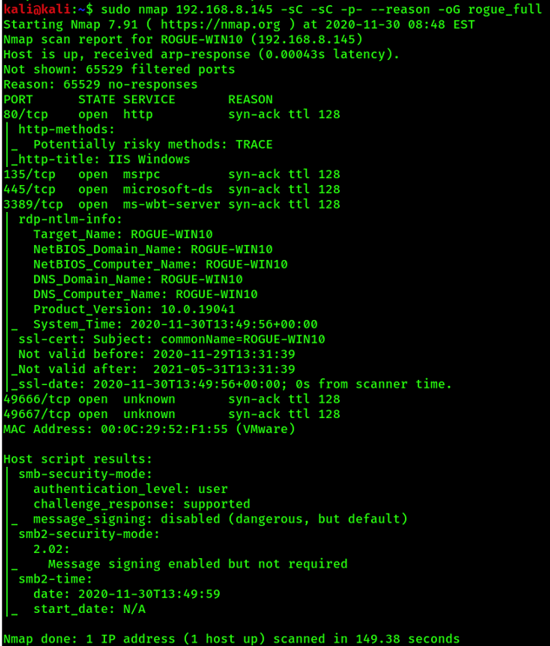
From the initial scanning and port enumeration on the examples above we can determine the following:
- It’s a Windows operating system.
- Ttl at 128 confirms it’s Windows.
- It’s a virtual machine running on VMWare per the MAC Address.
- Host name is ROGUE-WIN10, which might mean it’s a Windows Version 10.
- Remote Desktop is available.
- RDP confirms Windows version 10.0.19041.
- It has SMB version 2.
We also have information on ports:
- Port 80 – Windows endpoint running a Web Server
- Port 135 – Windows RPC
- Port 445 – Server Message Block (SMB)
- Port 3389 – Microsoft Terminal Server (RDP) officially registered as Windows-Based Terminal (WBT)
This information shows a few potential areas of risk. The endpoint is running a web server which could mean potentially misconfigured websites. It has SMB enabled which, if unpatched, could be exposed to Eternal Blue exploit. RDP port 3389 could allow an attacker to brute force if the user is using a known or weak password. Remote Desktop Protocol (RDP) running on port 3389 enables a remote graphical connection to the Windows endpoint, which is known previously to have vulnerabilities such as BlueKeep (CVE-2019-0708).
With the increase in employees working remotely, Windows endpoints are now out in the wild
During the pandemic, there’s been a surge in RDP ports discovered. With the increase in employees working remotely, Windows endpoints that would have never left the office are now out in the public domain, aka the wild, wild Internet of Connected Things. In the office, endpoints would typically be protected by the corporate firewall. When they’re moved to the public internet those ports are exposed. If those endpoints don’t have a host-based firewall they’re most likely being actively scanned for open ports using the methods above.
How to Protect Against Active Recon
- Patch and update Windows endpoints. Focus on Remote Code Execution or high-risk CVEs to prioritize patches. I’ve found patch management is often a never-ending story that often looks like this:
Patch Tuesday
Test Wednesday
Pilot Thursday
Rollout Friday
Cry Saturday
Rollback Sunday
Redeploy Patch Monday
Patch Tuesday
- Uninstall or disable unused applications and ports. The fewer apps and services running on Windows endpoints, the fewer targets. With fewer things to look through, the more difficult the process is for an attacker and the more risks they’re willing to take, which increases the possibility of discovery.
- Use strong authentication. Use strong passphrases, multi-factor authentication, and privileged access security. Never let a password be the only security between an attacker and your Windows endpoints.
- Know what ports are running. Listen for connections in your environment. Actively scan and understand the risks of each.
What have we learned so far?
A lot, actually. At this point, we know what types of systems we’re dealing with and roughly what’s running on those systems. We can pause at this stage to take it all in and draw up our attack plan for the next stages of the ethical hack.
In Part II of this blog series, Hardening Windows Endpoints Against Cyberattack, I walk through steps 3-5 of the ethical hack (Service Enumeration, Access Exploitation, and Privilege Escalation), and you’ll find all the tools you need to pull everything together for a comprehensive endpoint security strategy.