How to prepare for upcoming 2023 NYCRR 500 requirements with Delinea
Deadlines are looming. The latest amendments to 23 NYCRR 500 raise the bar for financial entities in New York to demonstrate cybersecurity best practices.
NYCRR isn’t just about ticking off compliance checkboxes. The New York State Department of Financial Services (DFS) has recognized that ransomware and data theft commonly exploit identity and access-related vulnerabilities. In response, the latest amendments to the regulation, announced in November 2023, require financial firms to implement Privileged Access Management (PAM) best practices to safeguard customer data, prevent fraud, protect intellectual property, and ensure financial stability.
Don't risk penalties or losing your charter.
In this blog, you’ll learn how Delinea supports complying with multiple 23 NYCRR 500 requirements and how to set a strong PAM foundation that gives you the flexibility to add capabilities in stages. That way, you can address the most critical gaps in your compliance posture first, use your IT resources efficiently, and prepare your organization for successful adoption.
Who needs to pay attention to NYCRR?
23 NYCRR 500 covers regulated financial firms operating in New York State. There's a newly minted category—Class A companies—which comes with extra responsibilities.
Upcoming deadlines for your cyber program roadmap
As you develop your strategy to address the new amendments, you’ll want to have adequate security capabilities in place by the deadlines.
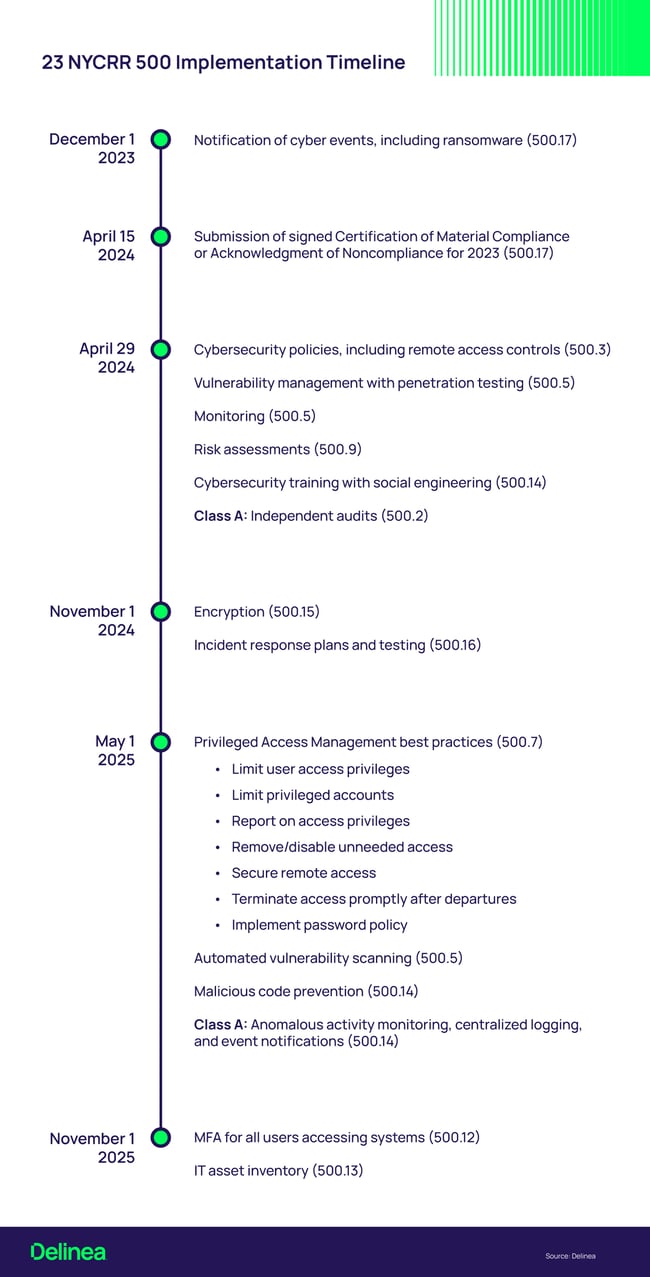
Sources: https://www.dfs.ny.gov/system/files/documents/2023/11/cybersecurity_implementation_timeline_covered_entities.pdf and https://www.dfs.ny.gov/system/files/documents/2023/11/cybersecurity_implementation_timeline_class_a.pdf
Delinea prepares you for NYCRR compliance now and in the future
Covered Entities and Class A companies need easy-to-use solutions for fast time to value. The cloud-native Delinea Platform makes PAM adoption seamless, so you aren’t installing new software or learning a new interface every time you deploy a capability. As your partner, Delinea streamlines your path to compliance, helping you address multiple 23 NYCRR 500 requirements.
| Section | Requirements | Delinea PAM |
| 500.3 | Cybersecurity Policy | Yes |
| 500.5 | Penetration Testing and Vulnerability Assessments | Yes |
| 500.7 | Access Privileges and Management | Yes |
| 500.8 | Application Security | Yes |
| 500.11 | Third-party Service Provider Security | Yes |
| 500.12 | Multi-Factor Authentication (MFA) for All | Yes |
| 500.14 | Anonymous Activity Monitoring and Training | Yes |
| 500.16 | Incident Response and Business Continuity Management | Yes |
Section 500.3: Cybersecurity Policy
Delinea’s PAM Policy Template helps you develop PAM policies to incorporate into your full cybersecurity policy. You can easily customize it and share it with IT teams, executives, and auditors.
Section 500.5: Penetration Testing and Vulnerability Assessments
Delinea integrates with vulnerability scanners to provide controlled and audited access to privileged credentials. This allows authenticated scans to run systematically, always having the correct credentials.
Section 500.7: Access Privileges and Management
With the Delinea Platform you meet this requirement by adhering to zero trust and least privilege best practices.
You can:
- Ensure password policies meet standards for length, complexity, and uniqueness.
- Secure passwords in an encrypted vault.
- Limit user access to provide only what’s needed for specific tasks, only for the period necessary.
- Require privilege elevation be approved and limited in time and scope.
- Eliminate broad or standing privileges, expired or unused privileged accounts, and local privileged accounts on workstations.
- Regularly review privileged access, disable permissions, and deprovision privileged accounts.
- Monitor all privileged activities.
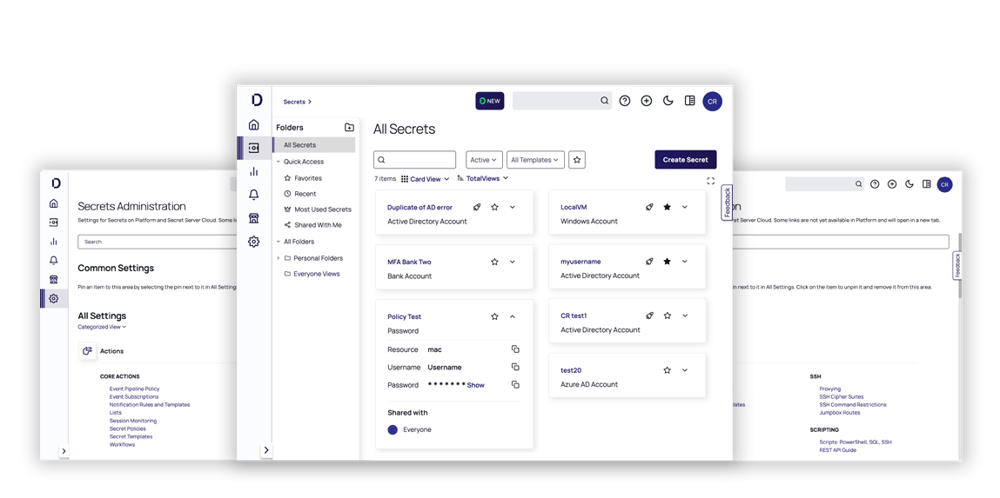
Delinea Privileged Access Management Solution
Section 500.8: Application Security
DevOps Secrets Vault supports secure development by managing credentials for applications, databases, CI/CD tools, and services and securing app-to-app communications and app-to-database access. You can centrally manage and audit secrets used within the development process, including access to tools for software and infrastructure deployment, testing, orchestration, and configuration.
Section 500.11: Third-party Service Provider Security
Remote Access Service provides a browser-based UI through which third parties outside your network can establish VPN-less remote sessions. Third parties don’t need to be joined to Active Directory to be managed by the central PAM solution. Their behavior is monitored and recorded.
Section 500.12: Multi-Factor Authentication (MFA)
The Delinea Platform offers flexibility and control to enforce MFA throughout the access chain, at initial login, checking out secrets, and privilege elevation. You can also enforce MFA based on risk signals, such as when a user demonstrates unusual privileged behavior, or as part of incident response.
Delinea's MFA at Depth for Privileges
Section 500.14: Monitoring, Malware, and Training
Anomalous Activity Monitoring
Session management, including real-time monitoring, recording, and reporting, increases oversight to mitigate the risk of privileged account misuse. Privileged Behavior Analytics creates a baseline for expected privileged user behavior and alerts you to unexpected, potentially malicious activities.
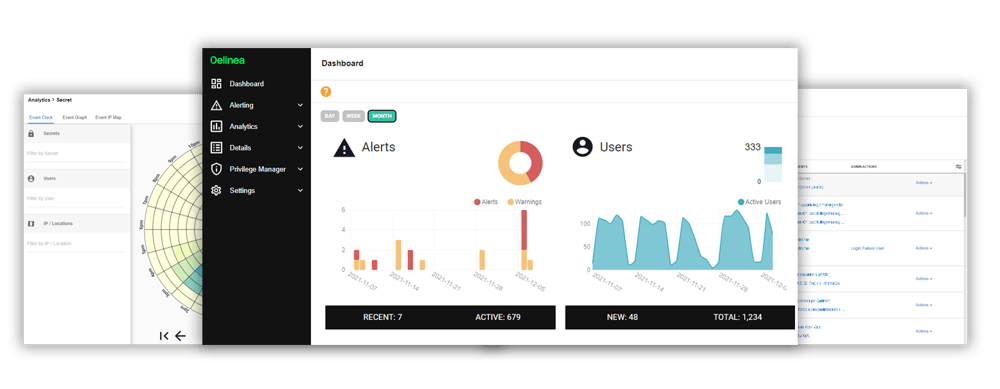
Detect anomalies in privileged accounts across your network
Malware prevention
Privilege Manager employs allow and deny lists for malware prevention. Users may only download applications or run scripts on allow lists. Known malicious applications are automatically added to deny lists through built-in threat intelligence. You can sandbox unknown applications that may contain malicious code for investigation.
Cybersecurity awareness training
Delinea has numerous resources to educate users on password best practices, access policies, malware prevention, and more. Cybersecurity for Dummies covers the essentials.
Section 500.16: Incident Response and Business Continuity Management
Delinea’s incident response plan template contains a checklist of roles, responsibilities, and steps to contain identity or access-related incidents before they damage critical systems.
Ready. Set. Go!
Even if you’re not a financial institution operating in New York State, consider 23 NYCRR 500 a harbinger of future regulations. Other state and national regulatory agencies look at this approach as a best practice and are likely to follow suit.
Implementing comprehensive cybersecurity measures can be daunting. Let us know how we can help.
*Please refer to the cybersecurity regulation for full text of all requirements. I highly recommend subscribing to DFS Cybersecurity Resource Center for ongoing updates.



