Why granting least privilege for servers should be on your radar
Least privilege is the principle of providing users, processes, and systems with only the minimum level of access necessary to perform their duties for as long as they are needed. For servers, it means restricting the privileges of admin accounts, services, and users (either single or group) to the bare minimum needed to function properly to get the job done.
Implementing least privilege for servers is crucial in today's digital landscape because it can help prevent diverse types of cyberattacks, such as malware infections, data breaches, and privilege escalation attacks
When servers have unnecessary permissions or privileges, attackers can exploit those privileges to gain access to sensitive data, execute unauthorized code, or take control of the server. Moreover, servers are often targets of sophisticated cyberattacks, and even a single misconfiguration or unpatched vulnerability can lead to a significant breach. Implementing least privilege can help mitigate the risk of such attacks and reduce the impact of any security incidents that do occur.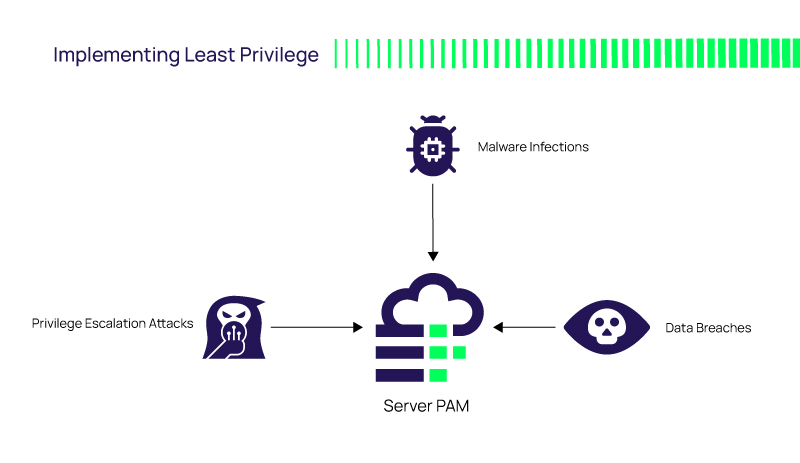
Least privilege is important for servers today because it helps organizations support a secure, stable computing environment, and reduce the risk of cyberattacks.
Eight big reasons why you should consider adopting least privilege for your servers:
- Compliance: Many regulations, such as PCI-DSS (Payment Card Industry Data Security Standard), HIPAA (Health Insurance Portability and Accountability), and GDPR (General Data Protection Regulation), require organizations to implement least privilege as part of their security policies. Compliance with these regulations is crucial for avoiding penalties, fines, and legal liabilities.
- Insider threats: Least privilege helps prevent insider threats by limiting the access of employees and other insiders to only what is necessary for their job functions. This reduces the risk of accidental or intentional misuse of privileged access.
- Complexity reduction: Servers can become complex and difficult to manage when users or processes have unnecessary privileges. Implementing least privilege simplifies server administration by reducing the number of permissions and access rights that must be managed.
- Risk reduction: Least privilege helps reduce the overall risk to an organization by reducing the attack surface and limiting the damage that can be caused by a successful attack. It also helps prevent data loss or corruption, which can be costly to recover from.
- Privilege escalation prevention: Least privilege helps prevent privilege escalation attacks, which occur when an attacker gains access to a low-privileged account and then uses that access to escalate their privileges and gain control of the system. By limiting the privileges of user accounts and services, you can prevent attackers from escalating their privileges and taking control of your servers.
- Protection against zero-day exploits: Zero-day exploits are vulnerabilities in software or systems that are unknown to the vendor or security community. By limiting the privileges of applications and services, you can reduce the risk of these vulnerabilities being exploited, as attackers will have limited access to the system.
- Improved auditability: When you implement least privilege, it becomes easier to track and audit the activities of users and services on your servers. This can help you detect and investigate suspicious activity more easily, as well as ensure compliance with security policies and regulations.
- Better resource utilization: By limiting the privileges of applications and services, you can prevent them from using more resources than necessary. This can help improve the performance and stability of your servers and reduce the risk of resource exhaustion attacks.
Implementing least privilege for servers is essential for supporting a secure, compliant, and efficient computing environment.
Delinea's Server PAM (Privileged Access Management) solution controls privileged access to servers in both on-premise and cloud/multi-cloud environments. Server Pam enables humans and machines to seamlessly authenticate with passwordless login, enforce least privilege with just-in-time privilege elevation, prevent lateral movement, increase accountability, and reduce administrative access risk. Check out the latest release of Cloud Suite, part of our Server PAM solution.
Get more information about our Server PAM solution.
Privileged Access Management Software for Servers


