SHIELDS UP = Recheck Your Security to be Incident Response-Ready
The stability of the world has significantly eroded in the past few weeks with the catastrophic war that has caused devastation and a humanitarian crisis in Ukraine. Our thoughts and prayers are with all the people impacted by this unnecessary destruction and hope that the world finds a peaceful end to it.
“Like many global companies, Delinea is proud to have team members based in Ukraine. In fact, we have an amazing and valued team in Ukraine that is on the minds of the rest of the Delinea team around the world...Thankfully, as of the writing of this blog, all our team members are safe. We continue to check in with them daily, although that is becoming more difficult as the war continues.” - Delinea CEO Art Gilliland
As the war on the ground continues to escalate, the information war is also intensifying. The battle rages between truth and propaganda, with cyberattacks as powerful weapons.
Cyberattacks are Weapons of War
Wars today almost certainly include cyberattacks that attempt to weaken adversaries.
While bombs and traditional warfare have geographic targets, cyber weapons can easily spiral out of control through connected systems and supply chains, as we have seen with major ransomware incidents such as NotPetya.
While the world is watching, this cyber crisis could easily escalate. Now is not the time for complacency. We must be more vigilant than ever.
Source: https://blog.f-secure.com/podcast-cyber-warfare-mikko/
I highly recommend listening to Mikko’s Cyber Warfare podcast, as it reminds us of the impact and use of cyber weapons.
Cyberattacks on Ukraine extend to NATO
According to Symantec’s Threat Hunter team, a division of Broadcom Sofware, destructive malware such as disk-wiping Trojan.Killdisk, and HermeticWiper were used to target organizations in Ukraine in the months prior to the invasion.
Cyberattacks spilled into Lithuania and Latvia, both NATO countries, resulting in damage to several targets including organizations in the financial, defense, aviation, and IT services industries. These attack patterns confirm how cyberattackers can easily gain access, bypass security controls, and move laterally through connected systems, including multi-national supply chains. These reports also demonstrate how cyberattacks disrupt critical public services such as financial and communications systems, across borders.
The cyberattacks impacting NATO member states raised questions regarding article 5 of the North Atlantic Treaty, which stipulates that an attack on one can be considered an attack on all and justifies the use of self-defense tactics In response, the NATO Cyber Defense Center of Excellence released a publication regarding the blurry but consistent position of NATO on cyberattacks against NATO countries.
Ransomware Misdirection and State-Supported Cyber Criminals
Not all ransomware attacks have the same motive. While most ransomware attacks are used for monetary gain, some ransomware gangs have declared nation-state allegiance using ransomware attacks as a decoy or disguise. One example is WhisperGate, a wiper-like worm with similarities to NotPetya but no intention of demanding money. Rather, its motive is to disrupt essential services. Such tactics are commonly used by governments to maintain deniability, and using state-supported cyber criminals or cyber mercenaries is a way to distance themselves from cyberattacks that target civilians.
CISA (Cybersecurity & Infrastructure Security Agency) Warns: “SHIELDS UP”
While there are no specific or credible threats at this time to governments or organizations outside of Ukraine, it is important to stay vigilant, prepare, and ready your incident response plan. Review the CISA guidance and check whether you are ready.

CISA’s Shields Up guidance provides the following essential information:
- Guidance for All Organizations
- Recommendations for Corporate Leaders and CEOs
- Ransomware Response
- Steps You Can Take to Protect Yourself & Your Family
- Additional Resources
Here's a summary of ‘Steps you can take to Protect Yourself and Your Family’:
- Implement and use Multi-Factor Authentication on your accounts
- Update your software and use automatic updates
- Think before you click
- Use strong passwords
Check Your Security Defenses and Raise Your Fences
Organizations should take time to ensure their security defenses are working. It might be a good time to increase your security sensitivity. Check for any suspicious activity in your audit logs, look for abnormal usage of privileged accounts, force verification and multi-factor authentication for sensitive systems, and remind employees to be cautious about suspicious emails or phishing attempts.
Know the early warning signals and indicators of compromise. Proactively check for any red flags:
- Excessive failed login attempts
- Unusual password activity
- Activity demanding a sudden increase in bandwidth
- Excessive activity outside of business hours
- Multiple logins with the same privileged account over a short time period
- Privileged accounts being accessed from unexpected IP addresses or countries
- Event logs with suspicious activity and event ID’s
Going From an Incident Response Plan to Being Incident Response-Ready
A solid incident response plan helps protect what matters most.
Businesses are often ill-prepared to deal with incidents, especially if an attacker has masqueraded as a privileged user—you may not know they’re doing any damage until it’s too late. Make sure your organization has an updated action plan.
Incident Response Plan/Checklist
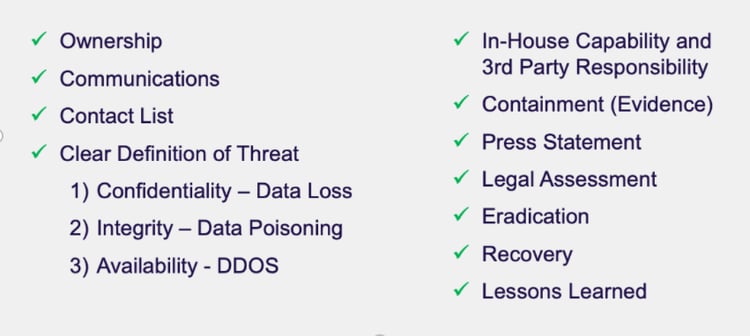
Above: An example of an Incident Response Checklist
Every organization needs a well-defined and tested incident response plan to combat cyberattacks. How well you define and test your plan can make the difference between simply having a plan and responding quickly and effectively to a cyberattack. Below are some examples of tasks that are often forgotten as part of an incident response plan, so it is important to review and simulate your cyber readiness.

Above: A plan is good, but being incident response-ready is best
Cybersecurity needs a business response, not just an IT or security response. When cyberattacks strike they impact the entire business and in some instances, the business comes to a complete stop. Therefore, the business must be prepared and ready to respond.
The world can change with the blink of an eye, so you can no longer put off high-priority security projects. It is a time to move from reactive security to proactive security and future-proof your security decisions. Take the time now to test your security resilience and responsiveness.
We must all work together to make the world a safer place both in the real world and online.

FREE TOOL
Cybersecurity Incident Response Template


