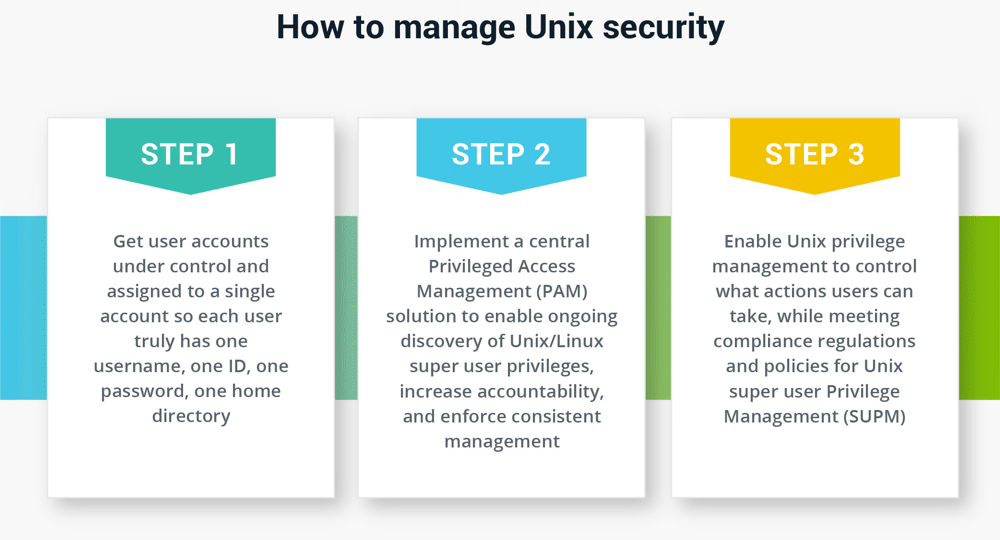
The approach we recommend
Step 1
The first order of business for Unix protection is to get everything in one place. To manage Unix security in a sustainable way, you need to get user accounts under control and assigned to a single account.
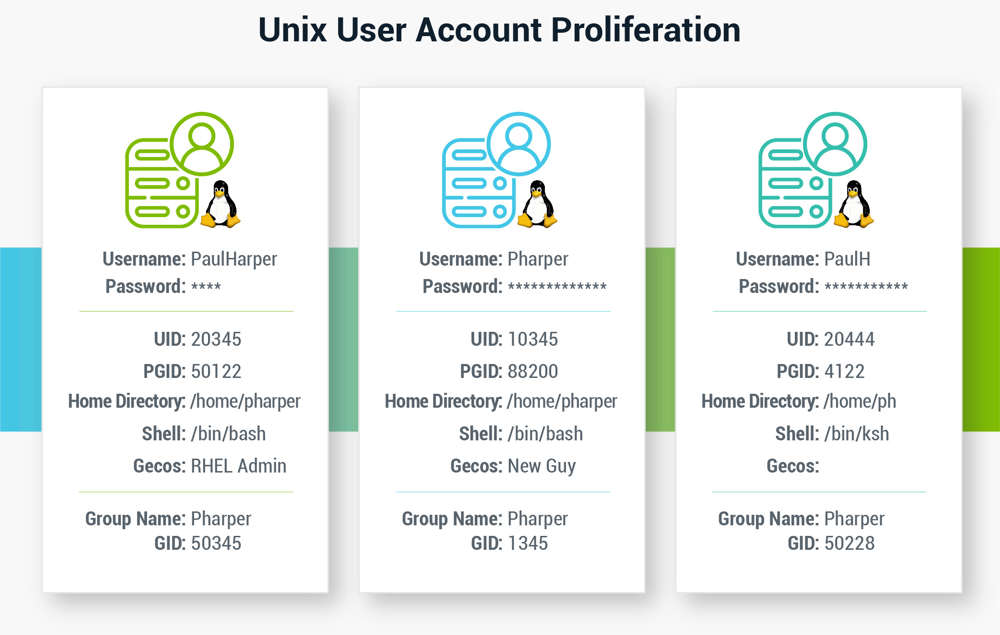
In a Windows environment, Active Directory (AD) allows this unification. AD leverages LDAP under the hood, but it largely uses Kerberos as the authentication protocol for Windows machines, so Unix devices struggle to integrate with AD.
An AD bridge extends Group Policy to non-Windows platforms so you can perform account maintenance and password updates for all systems through a single tool. With an Identity Bridge, you take advantage of consistent data across all of your systems. Each user truly has one username, one ID, one password, one home directory, etc.
Step 2
Once this type of identity unification is in place, a central PAM solution connects to your AD and lets you authenticate users and assign privileges with ease. PAM solutions enable the ongoing discovery of Unix/Linux superuser privileges to increase accountability and enforce consistent management. Immutable audit trails and enhanced controls, such as session monitoring and recording, provide oversight and simplify reporting and compliance.
Step 3
After a user is authenticated and logged in to your IT resources, Unix privilege management controls what actions they can take. Granular control of root credentials limits privileges while meeting compliance regulations and policies for Unix Superuser Privilege Management (SUPM).
You can reduce the risk of privileged account abuse or accidental error by restricting commands based on defined policies and limited superuser permissions. SSH command allowlist allows admins to log in as root, but only gives them access to a set of predefined commands. For example, a Unix allowlist might mean IT administrators might be able to restart the database and read log files, but not reset user passwords.
Benefits of a unified privilege management/PAM system for Windows, Mac, and Unix
Most organizations have a mix of different operating systems for different functions. Some teams will always prefer Unix and Linux to Windows or Mac due to their flexibility as well as their open-source nature. As a security leader, you need to include all types of IT systems and all parts of your organization in your security strategy and ensure they follow security policies consistently.
You can support the different operating system groups within your IT organization and manage a comprehensive privileged security strategy with advanced least privilege solutions. Users like this approach because they no longer have to remember multiple credentials to log onto each of their systems.
A central PAM solution reduces the risk and complexity of managing a heterogeneous environment. It provides the benefit of common security policies and practices across groups. Preparing reports for management and audits become a simple, repeatable process. Now, when you need to revoke access when an employee leaves your organization, you can manage it with one step and include all systems.