One of the main advantages of using a cloud platform like AWS is that you don’t need to worry about maintenance and upgrades. Yet, cloud partnerships don’t absolve you of protecting sensitive information and processes. When you consider that Forrester Research found that 93% of enterprises are storing sensitive data in the cloud, you can see why the cloud is an attractive target for cyber attackers.
The AWS Shared Responsibility Model is blunt: “Businesses are still responsible for confidentiality, integrity, and availability of their data in the cloud.” The division of responsibility is pragmatic: cloud platform providers will enforce the security of the cloud, while customers are responsible for security in the cloud. In other words, customers must configure their cloud instances appropriately to enforce their desired level of security.
This is easier said than done. According to Gartner, “through 2023, at least 99% of cloud security failures will be the customer’s fault.” Cloud platforms make it their business to ensure the underlying platform has appropriate security protocols in place.
More than 77% of all cloud breaches involve compromised credentials
IT and security teams simply can’t protect cloud privileged accounts the same way they manage on-premise ones. Outdated security models are partly the reason why 80% of organizations operating in the cloud experience at least one compromised account each month, reports McAfee. In fact, more than 77% of all cloud breaches involve compromised credentials, warns the latest Verizon Data Breach Report.
You must control how cloud platforms are accessed and monitored in your organization.
Cloud platforms are only partly on IT’s radar
While most organizations have one preferred cloud platform (be it AWS, Google Cloud, or Azure), it’s not uncommon to dabble in more than one, especially if developers and other teams set up and manage cloud resources directly.
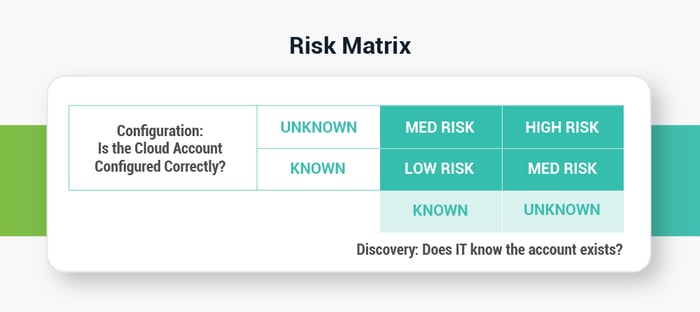
Misconfigured instances pose a high risk, yet IT must know the account exists before they can confirm they are correctly configured.
Privileged accounts for cloud resources are created quickly and may be abandoned just as quickly. With such a fluid process, it’s difficult for security teams to stay on top of how many privileged accounts have access to cloud resources, make sure they’re set up properly, and remove them when they’re no longer needed. To match the fluid nature of these accounts, continuous cloud account discovery is an essential cloud security control PAM teams need in their arsenal.
Cloud discovery is the first step
You must be able to discover cloud privileged accounts just as you do on-premise privileged accounts.
When you don’t know where privileged accounts exist, you may be leaving backdoor accounts in place that allow users to bypass proper controls. External threats may create privileged accounts for later access that can go undetected for months.
PAM designed for the cloud helps you increase the visibility of all types of privileged accounts. Cloud Discovery makes it easy to find privileged accounts in the cloud so you can set policies to manage them appropriately.
Delinea Secret Server can automatically find cloud privileged accounts and map existing secrets. Continuous AWS account discovery and Google Cloud discovery identify accounts used on those resources.
Secret Server alerts you when unexpected cloud accounts are found, so you don’t have to worry about gaps in a point-in-time discovery process.
Once you know which cloud accounts are used, you can make sure they are configured correctly.
Cloud Configuration
Analyzing billions of anonymized cloud events, McAfee found organizations typically have at least 14 misconfigured IaaS instances running at any given time, resulting in an average of 2,269 misconfiguration incidents per month. These can be as simple as forgetting to check a box during setup.
The most common misconfigurations include:
- Unrestricted access
- Lack of inbound and outbound data encryption
- Failure to turn on Multi-Factor Authentication (MFA)
On top of these issues, 5.5% of all AWS S3 buckets are misconfigured. Most organizations have at least one AWS S3 bucket set with “open write” permissions, giving anyone and everyone access to inject data into cloud environments, including malicious code that could modify records.
PAM solutions are designed to enforce consistent PAM best practices every time a new cloud account is set up, whether that’s by the security team, the infrastructure team, or a single developer building an application.
When you set up compute resources with there are several actions you can take to reduce risk:
- Secure cloud privileged credentials in a PAM vault
- Automate high-speed Secret creation, archiving, retrieval, and rotation
- Limit access to the cloud platform control panel
- Confirm MFA is required for root access
- Set up session monitoring and recording for root account activity
- Add in workflow rules for approval or dual control