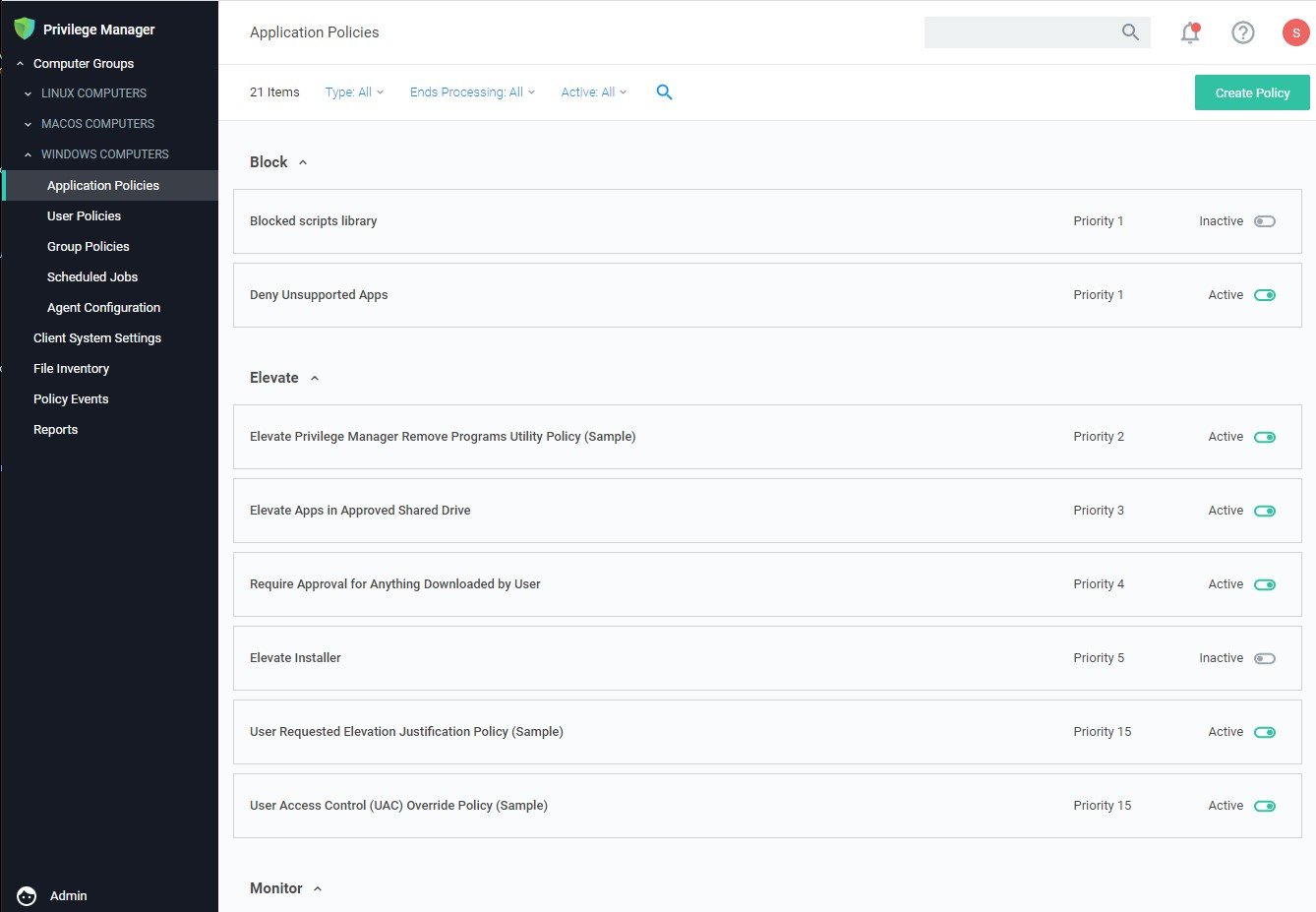
PRIVILEGE MANAGER FEATURES
Integrations
Ensure your endpoint management & application control solution works seamlessly with your other critical enterprise systems
- Active Directory & SCCM integration
- ServiceNow & ticket system integration
- VirusTotal & Cylance integration
Active Directory
For those organizations leveraging Active Directory (AD) or Azure Active Directory as their identity authentication and authorization service, deploying a least privilege program that works seamlessly with AD is absolutely critical. Privilege Manager integrates with AD so administrators can synchronize Domain Objects such as computers, OUs, and security groups from AD with their application control policies. Privilege Manager can leverage the user, group and privilege associations managed by Active Directory in its policy deployment and ensure unauthorized changes to AD made by endpoint users – such as adding a user to a local administrator account – can’t be blocked automatically and in real time.
Start a Free 30-Day Trial of Privilege Manager
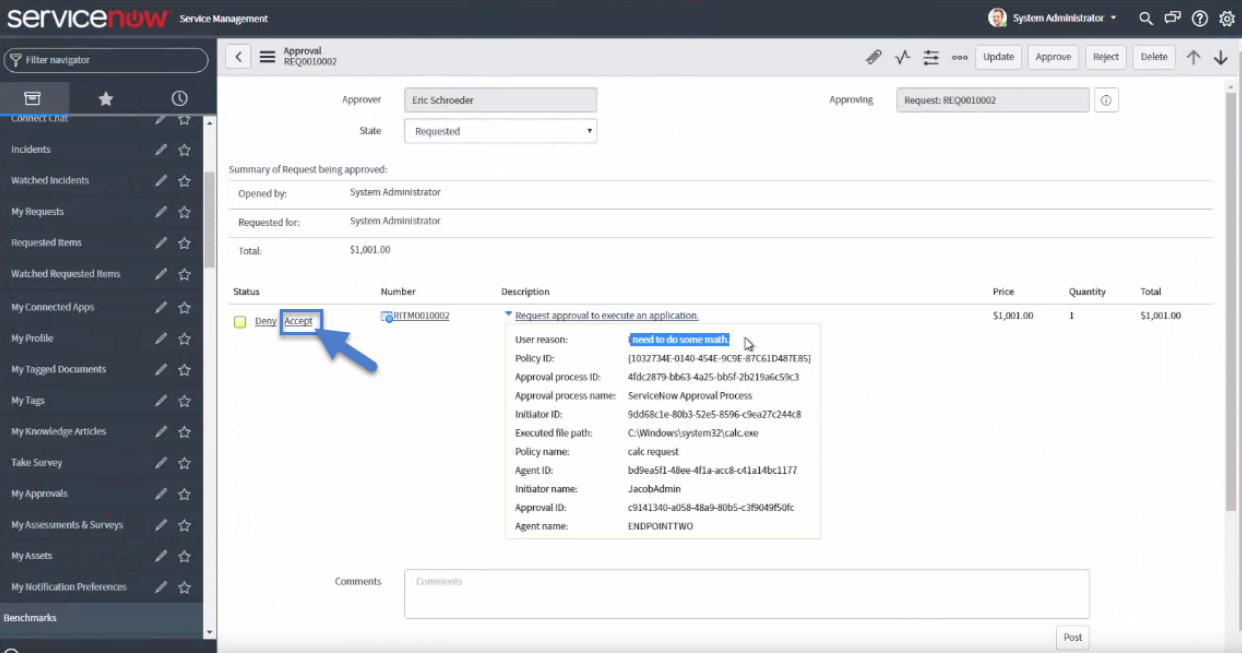
ServiceNow
Many organizations leverage ticketing systems to streamline their support workflow and like to view and report on all support requests within a single system. Privilege Manager can be fully integrated into ServiceNow, so support requests and IT responses can be managed, tracked, and reported via the ticketing system itself.
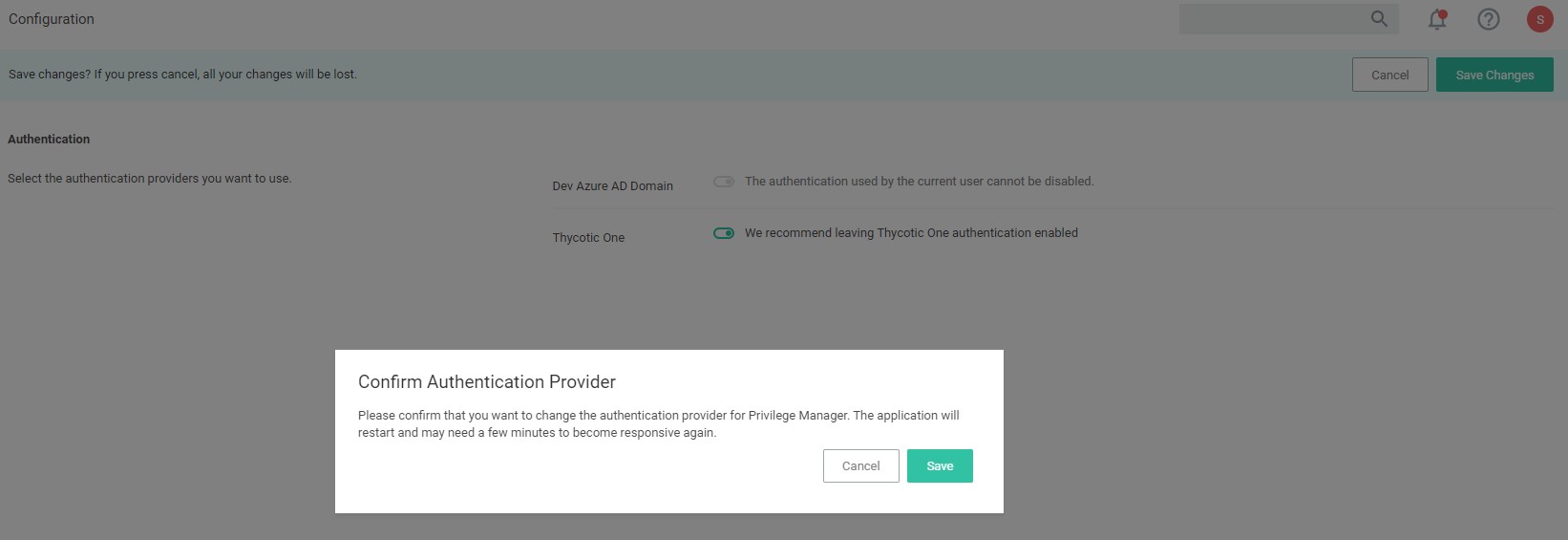
Secret Server
Secret Server and Privilege Manager work in tandem to provide privilege access security and tighten the attack surface. To ensure security for those accessing Privilege Manager, admins can use Secret Server as the authentication source for Privilege Manager to provide two-factor authentication (2FA) options. In addition, the local credentials managed by Privilege Manager can be stored in Secret Server.
Delinea also offers various methods of just-in-time privilege to allow users to automatically get approved elevation. With Secret Server’s check out hooks, administrators can provide time-based privileged elevation. Using the Request for Access feature, this process can be further secured with multiple approvers and ticket system validation. Privilege Manager uses policy-based controls to elevate applications’ users need without requiring administrator credentials or requesting IT support.
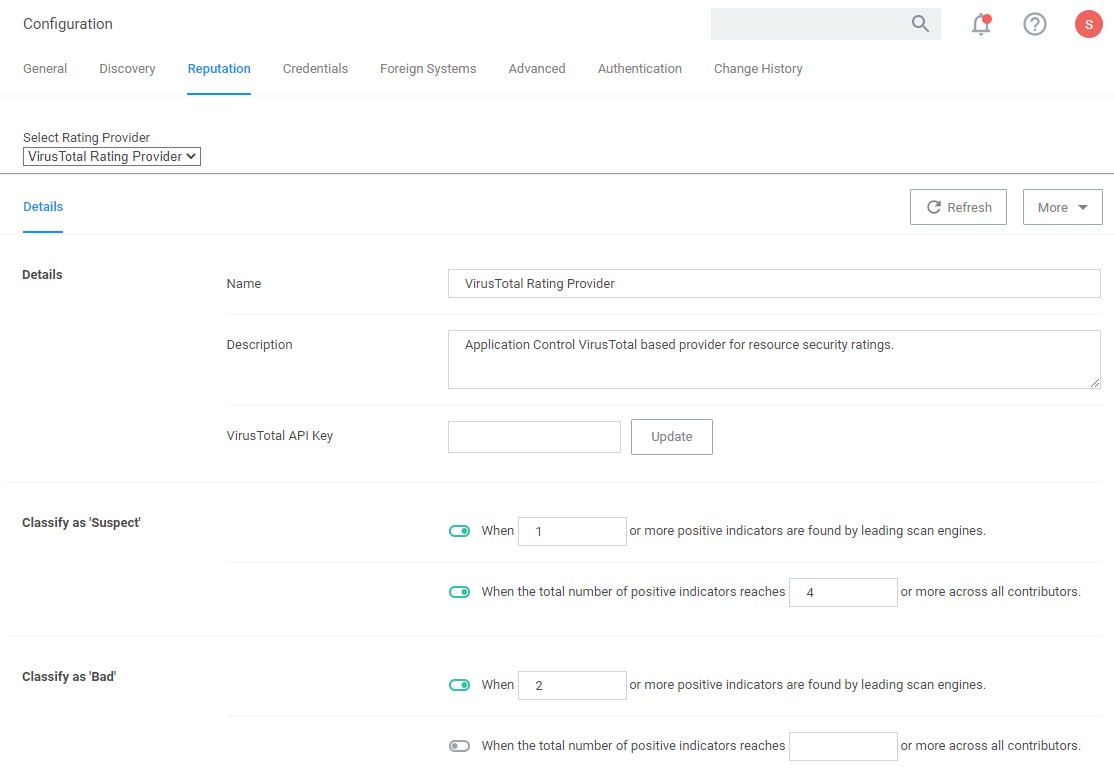
VirusTotal
People sometimes want to run applications and operations on their endpoints that are not on the your approved list of executables. To avoid productivity loss, these unknown applications can be evaluated by 3rd party file and URL analysis service to determine whether they should be allowed to execute. Privilege Manager integrates with leading service VirusTotal so all executables not explicitly on your allowlist or denylist can be evaluated in near real time.
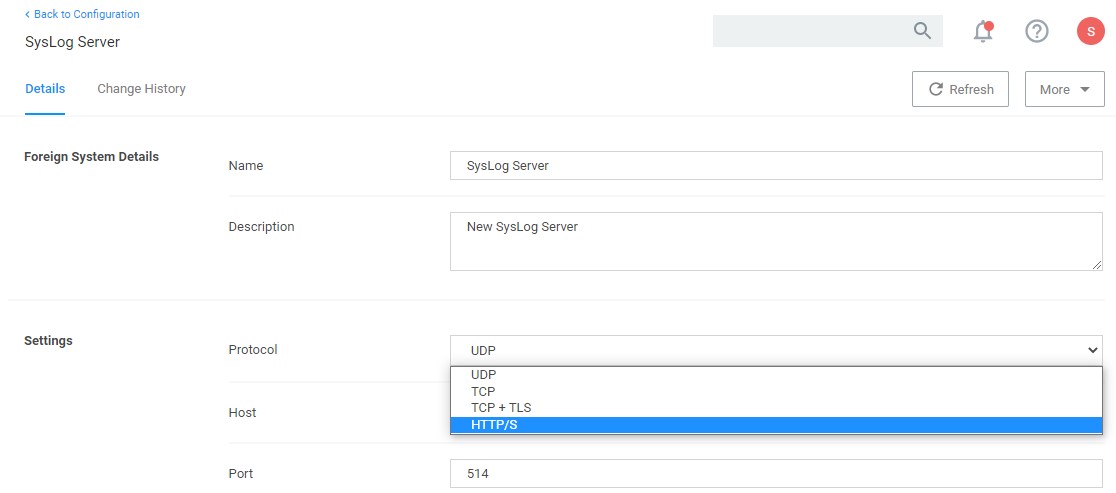
SysLog / SIEM
You can integrate your least privilege and application control program with a SIEM tool or other cyber security reporting and analytics services and tools. Privilege Manager can push out SysLog messages on a fully configurable schedule to any application or service that accepts the SysLog format.
System Center Configuration Manager (SCCM)
Privilege Manager can integrate with Microsoft System Center Configuration Manager and scan SCCM software delivery “packages” for applications that can be allowed by Privilege Manager.
Symantec Management Platform (SMP)
For those organizations utilizing the SMP solution for allowing and reputation, Privilege Manager can utilize the SMP allow and reputation engine to inform and prescribe its provision of application control capabilities across endpoints.
See these Privilege Manager features in action
Privilege Manager can automatically enforce your least privilege security posture through application control.