PRIVILEGE MANAGER FEATURES
Enterprise Readiness
Endpoint security and application control, with the performance and resiliency modern organizations demand.
- High Availability and Load Balancing
- Real-time application analysis
- Reverse Proxying
Public API
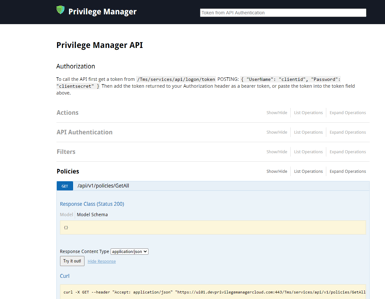
Privilege Manager’s public API automates bulk and repeatable operations by giving you the choice to manage the applications, actions, and components of policies without having to use the console.
Start a Free 30-Day Trial of Privilege Manager
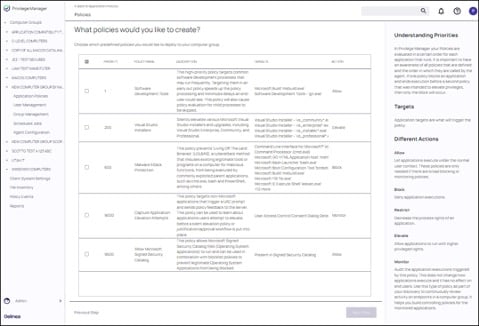
Workstation Policy Framework
The Workstation Policy Framework is an impactful feature that serves as the ideal starting point for every new user. Based on the most utilized policies by our customers, this framework enables quick and seamless deployment of essential policies, safeguarding your systems with ease.
It includes policies such as:
- Software Development Tools
- Visual Studio Installers
- Malware Attack Protection
- Capture Application Elevation Attempts
- Allow Microsoft Signed Security Catalog
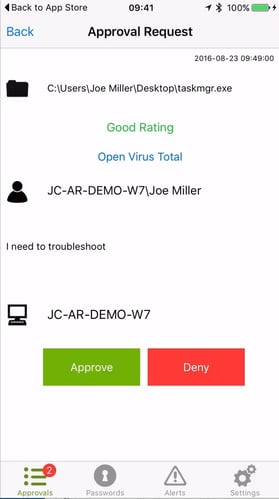
Privilege Manager Mobile Appx
The Privilege Manager mobile app for iOS and Android lets you manage endpoints, configure policies, process approvals, and receive event alerts via a mobile device so you can learn of requests and address issues quickly.
High Availability & Load Balancing
Web server clustering provides both high availability and load balancing by allowing multiple web servers to run Privilege Manager software. A clustered environment is key in disaster recovery scenarios as you can automatically failover to a separate web server with no downtime. Additionally, performance can be improved through load balancing by having multiple servers processing requests simultaneously.
Reverse Proxying
Many organizations choose to protect their Privilege Manager web server by restricting it from direct outbound internet access. To secure your environment according to best practices, it is not enough to simply set your server offline because Privilege Manager still will communicate directly to agents across your network that DO have direct internet access; therefore attackers can potentially use the connection between your endpoint agent and Privilege Manager to breach your web server. To prevent this direct connection between agent endpoints and your Privilege Manager web server, Privilege Managers allows for the setup of a Reverse Proxy machine with limited.
See these Privilege Manager features in action
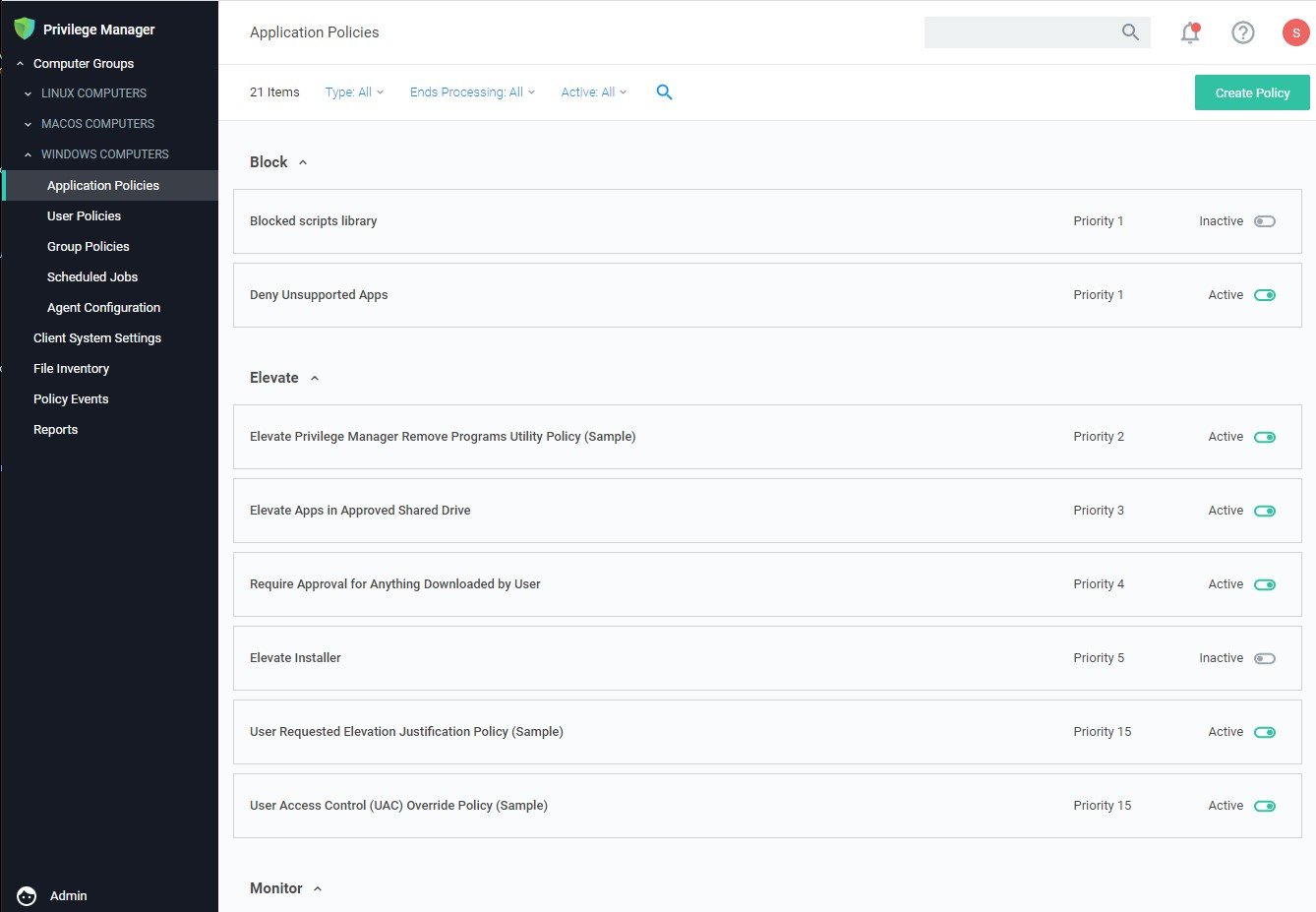
Privilege Manager can automatically enforce your least privilege security posture through application control.