Just-in-time and zero standing privilege
The way access works has fundamentally changed. AI agents operate autonomously, continuously, and across trust boundaries at machine speed. Developers move fast across cloud infrastructure, containers, and CI/CD pipelines. IT, security and developer teams face a tough balancing act. Granting too much standing access can unintentionally expose the organization to a breach. But too little access can cause user frustration and disrupt workflows.
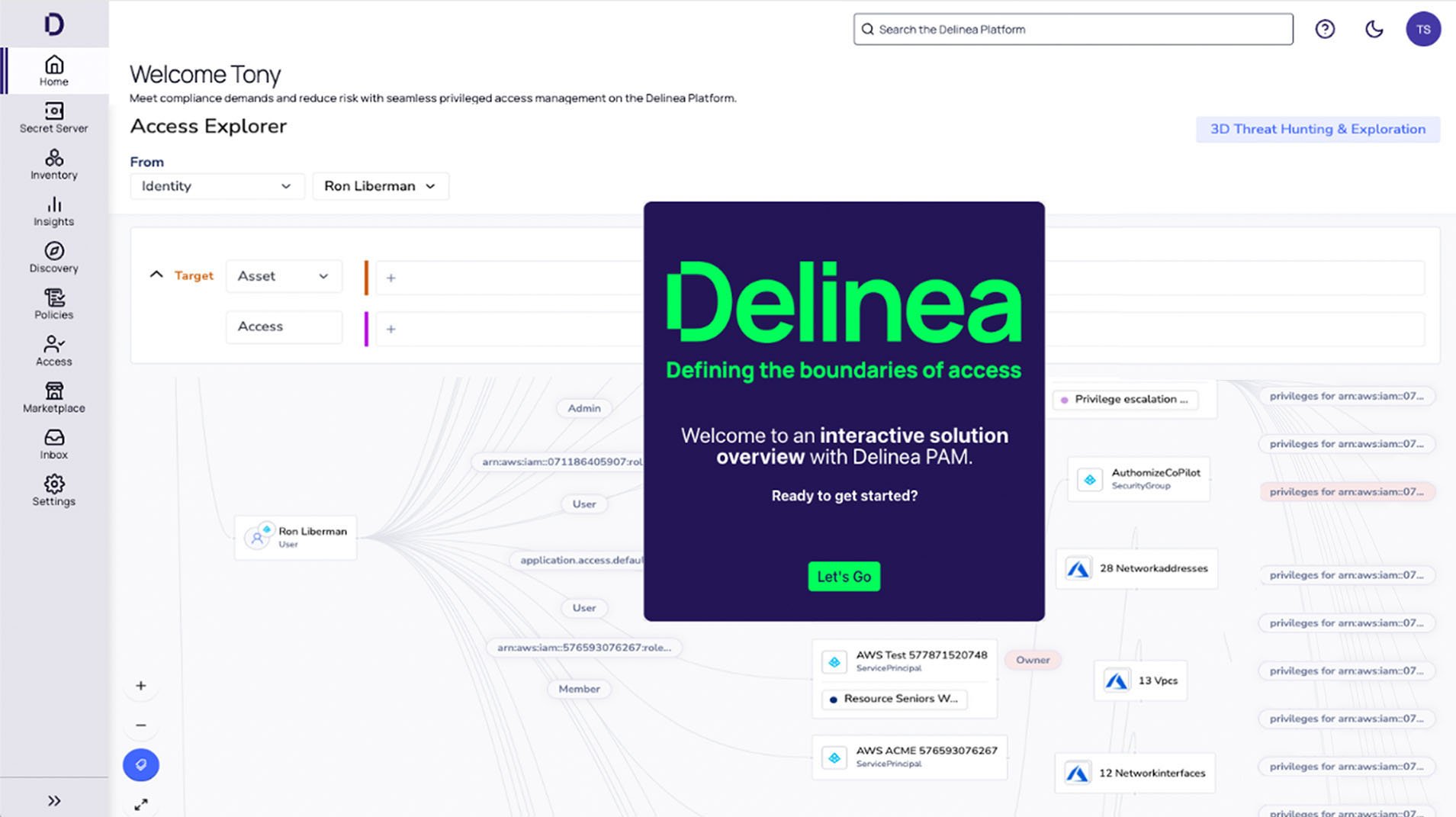
Delinea provides a modern Identity Security Platform to govern privileged access for every human and non-human identity across on-premise and cloud environments. Powered by Delinea Iris AI, it enforces least privilege at the moment of action, supporting both ephemeral and credential-based access models without forcing you to choose between them. This provides zero standing privilege (ZSP) capabilities to critical identities, effectively minimizing the attack surface while maintaining productivity. By implementing just-in-time (JIT) access, identities receive the precise access they need, exactly when required, and only for the necessary duration. Once the task is completed, access is revoked seamlessly until it is need
Deliver seamless access to users only when needed
Secure privilege in hybrid environments
Streamline and centralize secure server access
Secure local admin rights on workstations
Secure servers with cloud controls
Enforce just-in-time access for servers

Take the next step to secure all identities
The cloud native Delinea Platform reduces risk across human and machine identities with intelligent, centralized authorization, delivering compliant, usable identity security without slowing growth.